Companies all over the world in just about every industry rely on some form of technology for their day-to-day operations or processes. In fact, according to McAfee, the average business uses 1,427 distinct cloud services.
Whether it’s a project management tool that makes delegating workloads easier or intuitive payroll software that keeps the books on track, there’s no denying that technology helps modern businesses stay afloat.
However, with all this technology powering companies everywhere, the security perimeter has shifted. Cyber threats seem to be lurking around every corner, waiting to infiltrate. It’s important to make sure the data stored in every software program is secure. Critical company data that gets into the wrong hands could have detrimental results.
Protecting your company from data breaches comes with the territory of using advanced technology and is something that shouldn’t be taken lightly.
But how do you know if the software you’re using is actually secure?
Authentication: how do log in and authentication take place?

How users sign into programs is just as important as how data is stored, accessed, and kept safe. Two of the most common, secure ways to access a program are through single sign-on (SSO) and multi-factor authentication (MFA).
Single sign-on means that a user has one set of log-in credentials that can be used to access several apps, services, or portals. This streamlines access credentials for employees, so they don’t have to remember a different username and password combination for every program they need to access.
However, the catch with SSO is to create a username and password combination that is tough to guess or hack. Otherwise, hackers could have instant access to multiple programs that use those credentials.
To combat against that risk, multi-factor authentication (MFA) comes into play. With MFA, users are required to verify their identity by providing two or more evidentiary components that support the claim that they are who they say they are, which serves as an added layer of security.
MFA evidentiary components typically involve answering questions that only the correct user would know or, in addition to providing a password. An example could be providing a code or pin generated from another device or a fingerprint to access.
It’s critical to select software that will work with your existing systems. This will not only make it easier to integrate, but it will keep things as secure as possible.
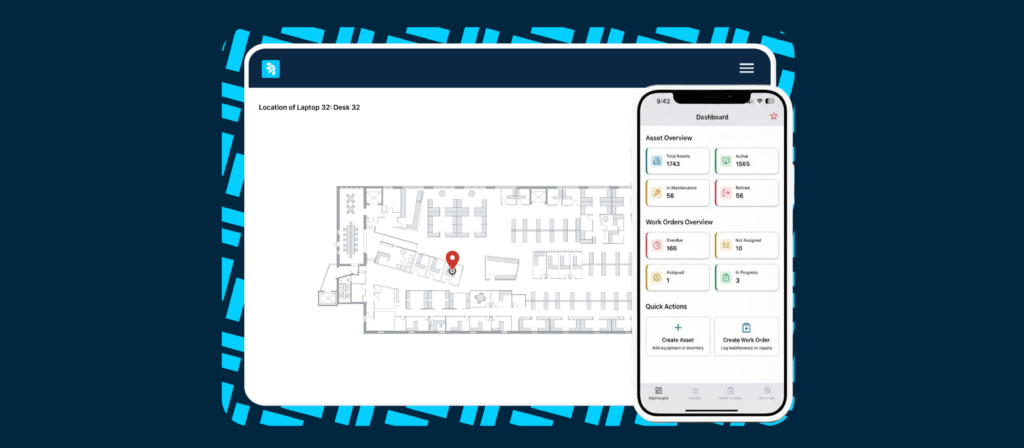
With OfficeSpace, implementation is handled through the systems you currently have in place. Our software syncs with some of the most widely-used directories including Okta, Microsoft ADFS, and OneLogin, so your team doesn’t miss a beat.
Data storage: how is your information kept safe?
It’s not enough just to prevent unauthorized parties from accessing your software—you have to make sure your data is secure where it’s stored.
Data storage is synonymous to data protection; if your data is stored in a secure place, then it’s protected from unwanted access or accidental data leaks. The method of where and how you choose to store your data must be able to scale with the volume of data you accumulate over time.
Data storage doesn’t just mean where or how it’s stored. It also includes how accessible that data is and how it can be manipulated and presented when needed, too.
Also, how quickly and easily authorized users can retrieve data is a significant part of secure data storage. Whether your team is remote, on-the-go, or working at headquarters, being able to safely and quickly access the information they need is imperative.
It’s essential to use a SaaS solution that prioritizes data security, access, and storage simultaneously. The data stored on the OfficeSpace platform is hosted and managed on servers that aren’t shared with other customers, which is uncommon for this type of program.
Data stored within the OfficeSpace platform is always backed up and is encrypted—both while data is in transit and at rest. You never have to worry about your data being at risk to threats or not being backed up.
Software updates: how and when do updates take place?

Does your SaaS provider offer regular and reliable software updates?
Whether you welcome them, hate them, or don’t care about them, continued software updates are crucial in more ways than you think.
Aside from providing you with the latest version of that software, updates help fix bugs or holes in the system that keep your data safe. Cyber threats and hackers prey on security flaws, and updates eliminate or correct those access points.
For example, you’ve likely heard of the Equifax data breach that put 143 million Americans’ information at risk. This information includes Social Security numbers, birth dates, and home addresses. Hackers were able to gain access to this data through Equifax’s system via a known vulnerability in a web application.
What’s worse?
A fix for this security issue was available a few months before the breach, but Equifax failed to upgrade the system.
It goes without saying that software updates could mean the difference between leaving data on the table, unsecured, and keeping it locked up from serious threats.
OfficeSpace customers can rest easy knowing that their data is always being stored on the most up-to-date version of the platform.
Can your SaaS solution do all that?
It’s clear that selecting software that can not only serve you but protect your data and grow with your company is vital to a successful SaaS solution integration.
You need a platform that can keep up with your daily operations and keep your data safe.
So where do you go from here?
Audit your current software and determine if improvements could be made. After all, the security of your company could be at stake.
OfficeSpace is competitive, forward-thinking, and invested in the security of its customers. Although we’ve been around for a while, we’re certainly up to speed when it comes to data and safety. And that’s why we’ve been able to make IT teams everywhere happy and secure.
Contact us today and a member of our team will help you determine the best solution for your needs.
Photo Credits: Grovemade, Patrick Lindenberg, Annie Spratt